By default, all outbound traffic that the Ecessa device receives from the LAN is subject to its session load balancing algorithm. As it receives an outbound session, the device will determine which WAN connection to use to transmit that session. This is determined by the uplink and downlink speed of each of the configured WAN connections, as well as the number of active sessions it currently has on each of those WAN connections at that time.
It may be necessary in some situations to override these default behaviors. The Static Routes page of the Ecessa device can be used to define default paths for specific traffic, while leaving the general load balancing intact.
Static Routes
There are two different types of Static Routes: Static Routes and Static Policy Routes. The type of route that should be used will be determined by how the outbound traffic is identified. The different criteria available for identifying traffic are: source IP address/network, destination IP address/network, specific protocol, TCP/UDP/IP source port and, TCP/UDP/IP destination port.
The following examples are based on this network:
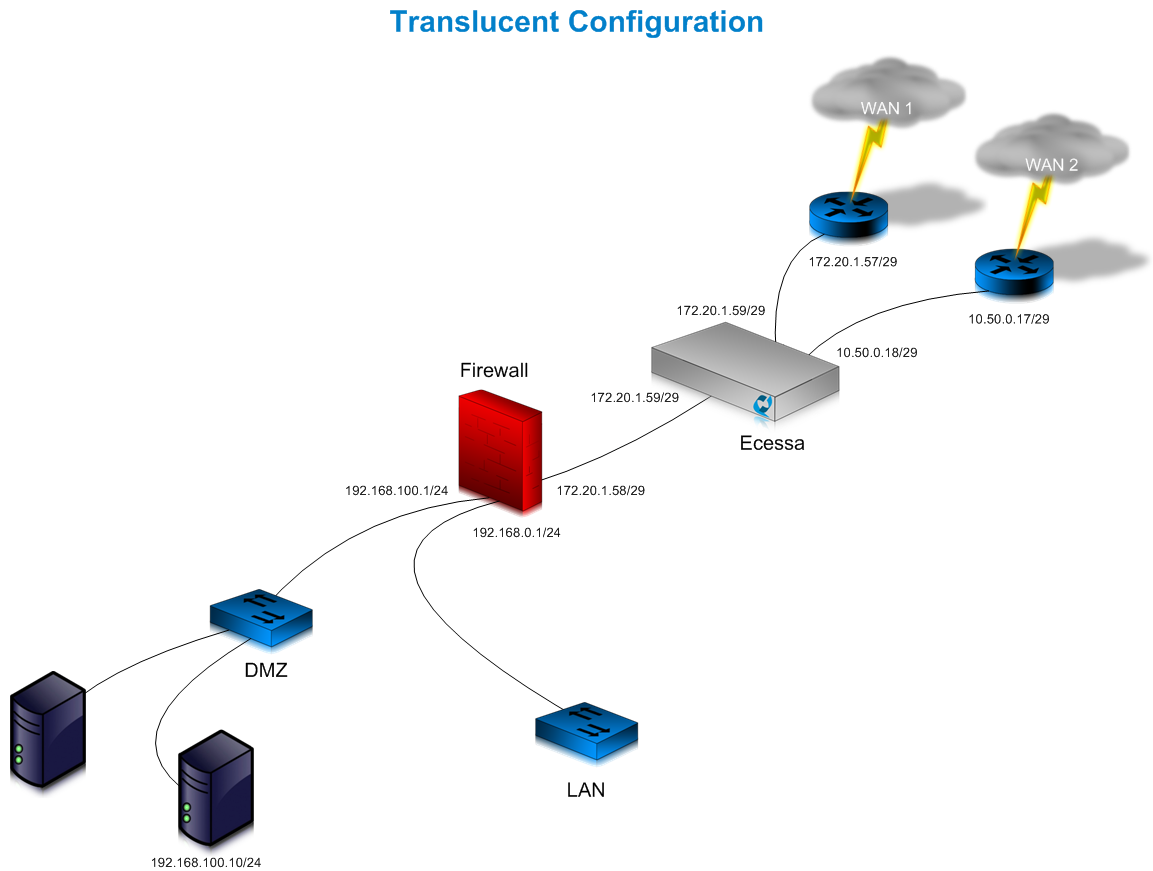
The example below shows the building of 3 separate routes: a route to a specific destination, a route based on a specific source IP, and a route for a specific type of traffic. There are differences between setting up Static Routes for Routed/Translucent Mode (Routed/Translucent mode static routes are entered the same way) and NAT Mode as illustrated below.
To set up a route to a destination network, which hosts a service the device connects to, using the original WAN connection, the set up would be a Static Route. A Routed or Translucent Mode network would appear as follows:
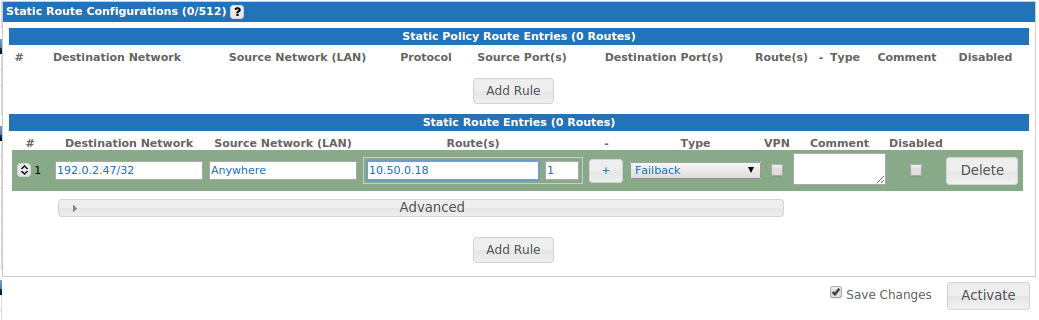
Please note: the "Route" IP is the interface IP of the Ecessa device on its Routed WAN. This is true for all Static Routes that are defined for Routed/Translucent Mode WAN lines.
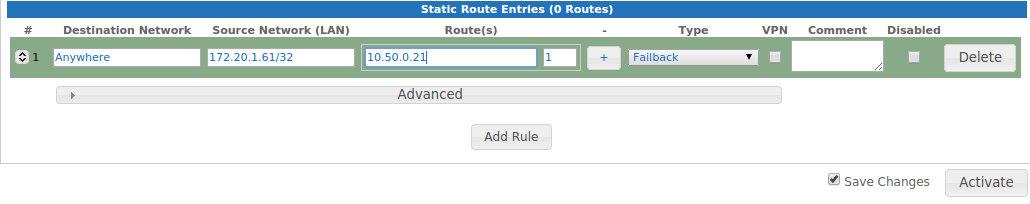
A NAT Mode configuration for a Static Route would appear as follows:
The difference is the IP address in the Route field. NAT Mode utilizes the IP address that the outbound traffic is translated to.
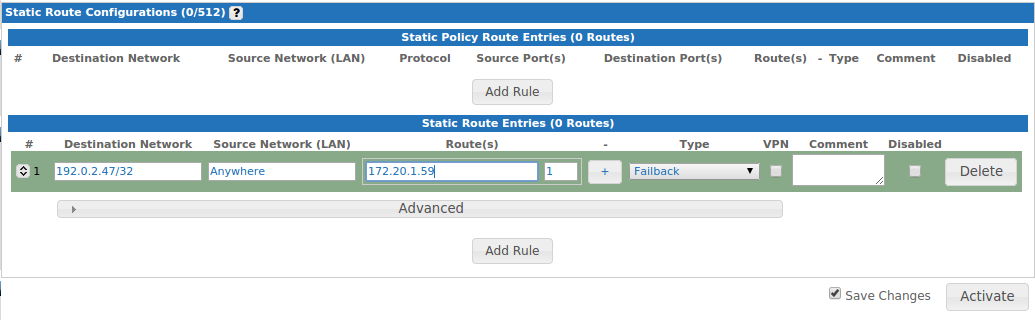
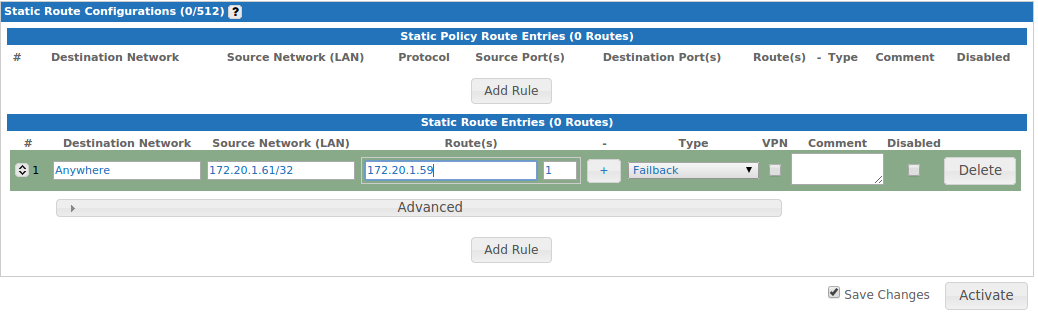
In both setups, the numerical box to the right dictates the order of failover. This field can be edited to achieve the desired order of failover.
Using the example diagram above, to define a Static Route for a server on the LAN (192.168.100.10) using the original WAN line, the configuration would be a Static Route using the IP address that the firewall rules define as the NAT IP address (172.20.1.61) of that server.
For a Routed/Translucent Mode configuration depicted in the above diagram, the route would appear as follows:
A NAT Mode configuration would appear as below:
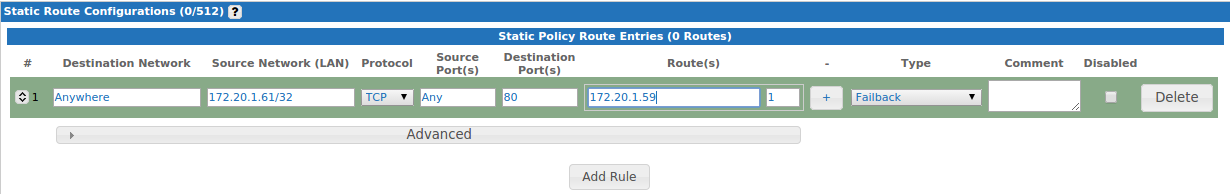
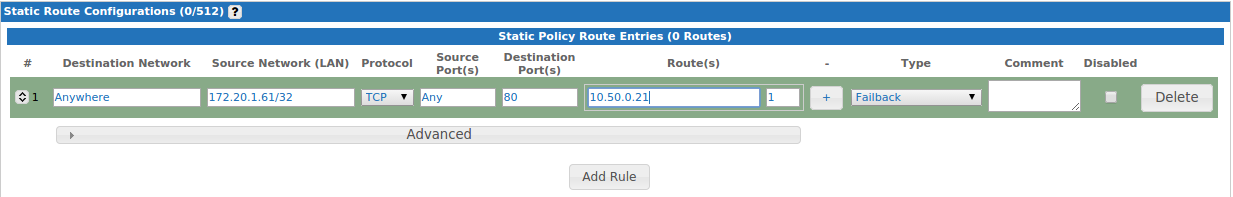
To define a Static Route to direct outbound traffic from a server on the LAN (192.168.100.10) over the original WAN line based on a protocol or port (HTTP, for example), the configuration used will be a Static Policy Route. This would utilize the IP address that the firewall rules define as the NAT IP address (172.20.1.61) of that server.
A Routed/Translucent Mode route configuration from our previous example would appear as follows:
A route in the NAT Mode configuration would appear as follows:
In almost all cases, Failback will be the preferred type of Static Route and should be selected from the dropdown. If your Static Route is being defined for a Site-to-Site VPN, select the VPN checkbox. The comments field allows you to create a description for the route.
Remember to click Activate to save changes made to the Static Routes.
This section illustrates how to configure a majority of Static Route scenarios; there are exceptions, which are not covered in this manual. If there are any questions about how to configure Static Routes in your environment, refer to our help page or contact Ecessa Technical Support at help@ecessa.com, or call (800) 669-6242 x 2.
0 Comments