Starting with software version 12.0.0, there has been a dramatic shift in the additional ways that SSL VPN users can be set up and authenticated. Versions prior to 12.0.0 only supported authentication of SSL VPN clients through the use of locally configured clients and certificates. For information on previous SSL VPN client authentication methods, see here.
With the improvements introduced in 12.0.0, administrators have a number of other options beyond using certificates. These new methods allow for username/password combinations through external authentication servers (RADIUS or Azure Active Directory) and the ability to add on additional Multi-Factor Authentication (MFA) through Duo.
It should be noted that the below are the only supported SSL clients at this time:
Windows:
-
OpenVPN GUI
-
OpenVPN Connect
Mac:
-
TunnelBlick
-
OpenVPN Connect
Chromebook:
-
OpenVPN Connect (app store)
We'll begin by discussing the two different methods to authenticate username and password.
RADIUS
First, you will need to create the Ecessa device as a client in the RADIUS server. This should consist of the Ecessa's IP LAN IP address and a secret.
Important: Keep record of this secret, as you will need it when configuring the Ecessa for RADIUS support.
Next, you'll need to verify the authentication protocols supported on the RADIUS server. The Ecessa currently only supports PAP and CHAP, so at least one of them must be configured as an allowable protocol on the RADIUS server.
We'll cover the configuration of the Ecessa itself in a later section.
AZURE ACTIVE DIRECTORY
First, if you do not have an Azure account, you will need to sign up for one here.
After you have an account, an Azure Active Directory tenant is required. To set up/learn more about tenants, you can go here.
Next, an Azure app registration set up within the desired Azure Active Directory tenant is required. To learn more about setting up the app registration, go here.
Note: If there are multiple Azure Active Directory tenants within your Azure account, make sure to switch to the desired tenant in Step 2.
Finally, the registered app must be configured to allow for Public Client Flows. To do this, after creating the application registration, click on “Authentication” within the “Manage” section. Under Advanced Settings->Public Client Flows, select Yes. Click “Save”.
Important: Take note of the application client ID and directory tenant ID listed on this page, as you will need them to configure Azure Active Directory on the Ecessa device.
CONFIGURING ECESSA SSL VPN FOR USERNAME/PASSWORD
On the Ecessa User Interface, navigate to the VPN section. Ensure that the Enable VPN box at the top of the page is checked.
Click on "Add SSL". Give your Security Association a name. Select your preferred protocol, either UDP or TCP. Ensure that "Connection Type" is set to Server.
Provide your local WAN endpoint(s) and your local LAN(s) that the VPN users should have access to.
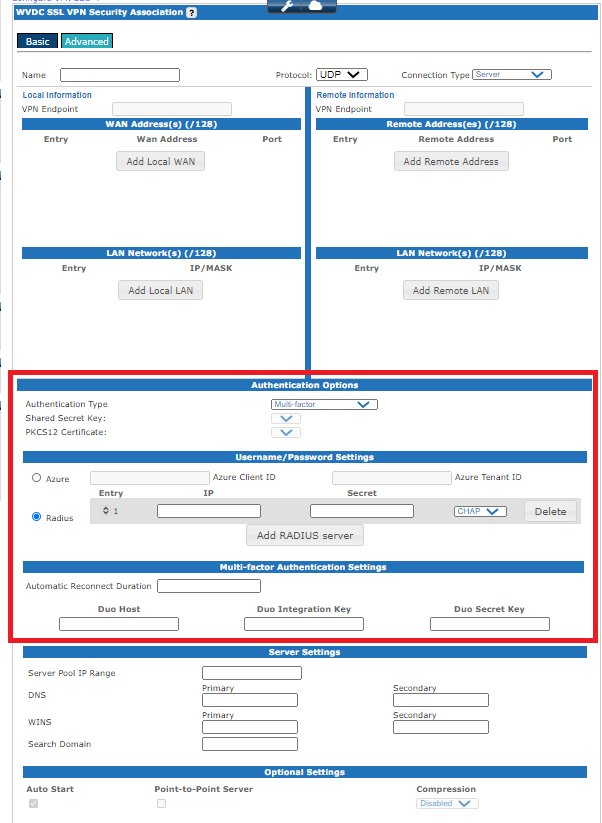
From the Authentication Options drop down, select either Username/Password or Multi-Factor. If selecting Multi-Factor, you will need to complete the steps in the Duo section below before you can finsh the VPN configuration.
Regardless of your selection, you will need to choose the Azure or RADIUS option. If you choose Azure, enter the Azure Client ID and Azure Tenant ID from the above Azure Active Directory section. If you choose RADIUS, click "Add RADIUS Server" and enter the IP address of the server as well as the Secret that was created in the above RADIUS section. Select the authentication method that was enabled on the RADIUS server (CHAP or PAP).
If you chose Multi-Factor, you will also need to fill in the fields in the "Multi-factor Authentication Settings".
Enter a "Automatic Reconnect Duration". This is the number of hours that an authenticated VPN client should be able to reconnect to the VPN after a disconnection without the user needing to perform full authentication steps. A value of 0 will force the user to perform authentication steps after any disconnection from the VPN server. Leaving the field blank will allow authenticated VPN clients to reconnect to the VPN server without the user perfoming authentication steps indefinitely.
You will then need to fill in the Duo Host URL field, the Duo Integration Key and the Duo Secret Key fileds. These would be determined when you set up Duo following the directions in the section below.
Fill in the "Server Settings" section with the IP Pool and DNS information for the clients, as well as any other information they may need.
If you wish to change the standard keep alive or encryption options of the VPN, click on the "Advanced" tab at the top of the page. Once you are finished, click on "Activate" at the bottom of the page. Your VPN is now ready for clients to connect.
DUO SET UP
This section is only applicable if an MFA VPN is to be used.
A Duo admin account is required. To sign up, go here.
It’s up to the customer/managed service provider to determine if there should be separate Duo admin accounts for different organizations of users in Duo. It’s possible to organize users with Groups in Duo, and separate authentication that way. But usernames from different organizations may have collisions if done this way.
The Ecessa VPN needs to have an Auth API application set up in Duo to function. To set this up, on the Duo web dashboard, go to Applications > Protect an application > Auth API -> Protect. If only particular group(s) of users should be able to authenticate with the Duo application, select the group(s) in the “Permitted groups” section. Take note of the Integration key, Secret key, and API hostname listed on this page, as they will be needed when configuring an MFA VPN on the Ecessa device.
In order for end users of the VPN to complete authentication through Duo, each end user must be fully enrolled in Duo (end user has an associated user in Duo with an MFA device registered). Ecessa does not currently support Duo inline self-enrollment through the SSL VPN. The Duo admin must add users in one of the ways listed here.
Whichever method is used to add/import/sync users, it should include an email address if the Duo admin intends to have the end user add their MFA device themselves (applicable for phones).
A Duo user’s username must match exactly with the username which is used for username-password authentication. For instance, if you chose Azure Active Directory in the above sections, the Azure AD UPN (User Principal Name) includes the domain, so using the above example, it would be tjohnson@ecessa.onmicrosoft.com. The associated Duo user needs to have this same full UPN as their username.
To learn more about Bulk Self Enrollment, you can go here.
To learn more about Manually Adding Users, you can go here.
EXPORTING RADIUS USERS TO DUO
RADIUS is generally set up with some external source of authority (mysql/local Active Directory/text file) which contains usernames and their passwords. It is possible to run RADIUS alone and have users and their passwords kept in a local text file, but this is not a recommended setup. In either case, the way to export RADIUS users into Duo is by converting the data from the external source of authority to a CSV file, which can be imported into Duo. To learn more about importing user into Duo, go here.
The only field required by Duo is the “username” field, but at least the “email” or “phone” field should also be specified in the CSV so that end users can be bulk enrolled (emailed/called). If neither is specified, the Duo admin would have to manually enroll every end user device.
SYNCING AZURE ACTIVE DIRECTORY USERS TO DUO
Duo supports automatic addition and syncing of users in an Azure Active Directory tenant. The procedure for this can be found here.
Note: Step 4 requires logging in to the Azure Active Directory tenant with a UPN (User Principal Name) corresponding to a user who has the global administrator role within the tenant. Use the UPN listed for the user within the desired tenant when logging in during this step.
For example:
If the tjohnson user has the global administrator role, and their home tenant is ecessa.onmicrosoft.com, and the directory to be synced is also ecessa.onmicrosoft.com, then you would login as tjohnson@ecessa.onmicrosoft.com.
However, if the tjohnson user has the global administrator role, and their home tenant is ecessa.onmicrosoft.com, but the directory to be synced is ecessaAD.onmicrosoft.com, then you would need to login as tjohnson_ecessa.onmicrosoft.com#EXT#@ecessaAD.onmicrosoft.com
Note: Leave “Normalize Usernames” unchecked. See the above “Duo Username Format” section for more information.
Important: Duo will only sync GROUPS of users from an Azure Active Directory tenant. So, users within the tenant must be first organized into groups before setting up syncing. To learn more about creating a group in an Azure Active Directory tenant, go here. You must add/authorize the Directory Sync entry and then select the groups to sync - otherwise "Sync Directory Now" will not sync any users.
0 Comments