The Virtual Tunnel Interface or VTI is a feature that allows for a more flexible VPN. A VTI VPN is a specialized type of IPsec VPN.
Advantages
- Simple to setup and integrate into the rest of the configuration
- More routing control - VTI can have traffic routed over it like any other WAN
- Improves scaling - fewer Security Associations than a multiple LAN VPN.
Disadvantage(s)
- Requires firmware 10.3+
- Might not be supported on the right (remote) endpoint.
The standard IPsec VPN encrypts traffic either for transport (host to host) or tunnelling (network to network). Tunnelling is the most common; one exception is WAN Virtualization.
The other exception is a VTI VPN, this allows the usage of Static Routes to send traffic over the VPN (same as WAN Virtualization); thus allowing failing into and out of a VPN.
This is unlike our standard IPsec VPN where local and remote LANs are specified - in this case the VPN is the first to route, no matter what, and thus not very flexible (VPN always wins).
With a VTI VPN you DO NOT add local or remote LANs to your VPN configuration (like you would in a Site-to-Site IPsec VPN).
This article goes into more detail on setting up a Site-to-Site IPsec VPN:
https://support.ecessa.com/hc/en-us/articles/200143806-IPSEC-Site-to-Site-VPN-tunnel
Also of note, for a VTI VPN you should only have one local and one remote WAN. To provide endpoint redundancy create multiple VPN SA's and use Static Routes to describe the failover precedence.
Once you have your VPN up, now it’s time to route traffic over that VPN.
VTI VPN Usage with a Static Route
It is just as simple as routing over any other WAN. When the VPN is up, we will route traffic over it. If not we failover to another VPN or WAN.
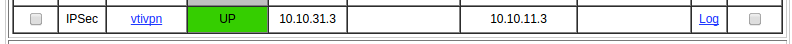
That is the VPN we want to use to statically route traffic destined to 192.168.10.0/24 over. We do this by using the VPN name as our “Route(s)”:
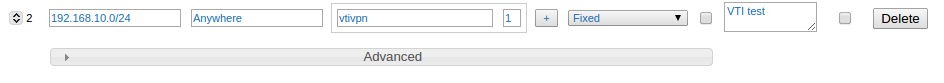
With that in place our traffic will now go over the VPN (the other side will need a similar route to return replies over the VPN).
In this case this traffic is fixed, since this subnet is in RFC 1918 reserved 192.168/16 space and cannot be routed over the internet*, and unless you have an MPLS, another VPN, or WAN Virtualization this traffic will fail. So we set the option Failover Type to Fixed.
*Same goes for the WAN endpoints being in the 10/8 which also won’t route over the Internet.
More information on Static Routes and Static Route Failover Type(s) can be found here:
Creating a Static Route
https://support.ecessa.com/hc/en-us/articles/200143396-How-do-I-create-a-static-route-
On Static Route Failover Type(s)
This can be used with Cisco, Checkpoint, Amazon VPC, and more devices.
References
Cisco Configuring a Virtual Tunnel Interface with IP Security
Checkpoint Check Point Security Gateway IPsec VPN to Amazon Web Services VPC
0 Comments