Once the Firewall configuration has been planned out, it can then be entered into the device.
At the top of the Configure Firewall menu of the Ecessa device there is an option to Enable Firewall. When this box is unchecked, the Firewall is not enabled and any configured policies will not be used. This is useful for cases where the Ecessa device is already in production and configuring the Firewall quickly would cause significant disruption. In this case, all of the Firewall configurations can be entered before the Firewall is turned on.
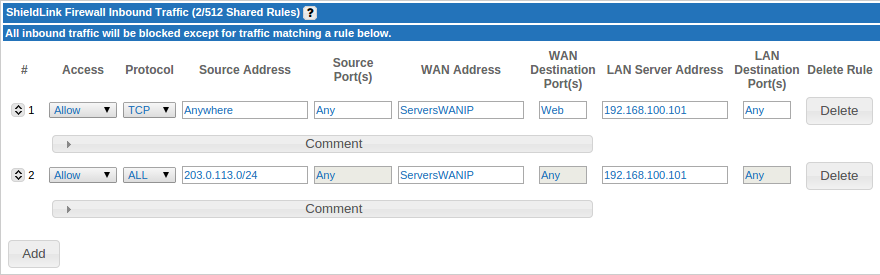
Firewall Inbound Traffic
The Add button at the bottom of the section is used to add a new entry to the list of rules. The Activate button is used to activate all new and changed entries in the section.
Also notice the [-] character at the top of this section. It is used to collapse this section, making it easier to see all configuration sections if the Ecessa device has a large Firewall configuration. On subsequent visits to the Firewall configuration menu, this section will usually be collapsed automatically. Use the [+] character to expand the section.

Advanced (12.2.0+)
The Advanced menu under each rule has two checkbox options:
IPS - This checkbox will allow the IPS feature to act upon these specific rules. Without this box checked, specified traffic will follow the rule regardless of the IPS configuration
Geoblocking - This checkbox will allow the Geoblocking feature to act upon these specific rules. Without this box checked, specified traffic will follow the rule regardless of the Geoblocking configuration
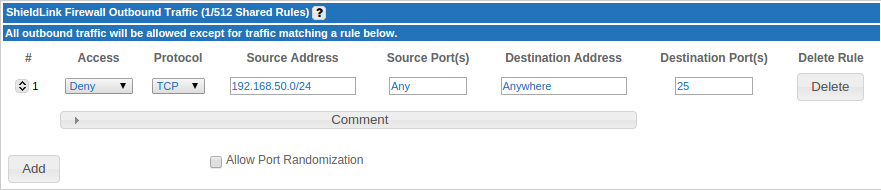
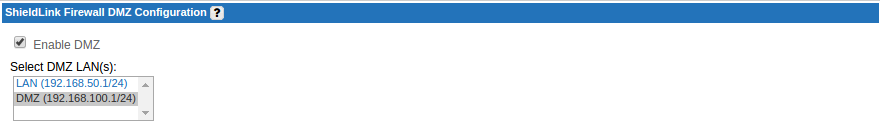
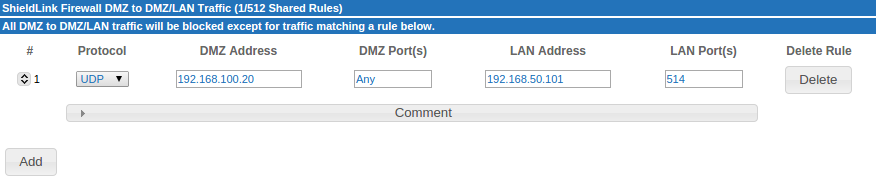
Firewall Outbound Traffic and DMZ to LAN Traffic
The Outbound traffic and DMZ to LAN traffic sections are configured in the same manner (below). At the top of the DMZ section there is a scrolling menu which allows you to select a LAN interface to be used as a DMZ. Once a LAN has been set as the DMZ, hosts on the DMZ are not able to connect to hosts on other LANs unless explicitly permitted by adding rules to the DMZ to LAN traffic section.
User Defined Aliases
Although Aliases are designed to make the Firewall configuration process less complex for the purpose of this document they have been left out in the above example. On the Firewall page you are limited by how many addresses/ports you can place on a single rule. With aliases you can define multiple different types of information for an alias, then on the Firewall page you can use this alias in order to extend the rule to all the configured addresses/ports.
Click on the "Aliases" link under the ”Basic Setup” section on the left hand menu of the web interface to add or modify aliases. For versions earlier than 8.2, use the “Configure User-Defined Aliases” link at the top of the Ecessa Firewall page to add or modify aliases.
Created below are two examples of Aliases that could be used as part of a Ecessa Firewall configuration. The first alias is an address type alias named ServersWANIP and references the two WAN IP addresses. The second alias is a port type alias named Web and references ports 80 and 443.

The Alias name would then be used in place of the actual address or port configured on Ecessa Firewall.
Once the entire Firewall configuration has been entered, we can check the Enable Firewall check box to begin using the Firewall configuration that has been entered. This document provides an overview of common Firewall configuration options. Please note: this is not a comprehensive guide. For a more complete understanding of all available Firewall options available on the Ecessa, please read the Firewall help page found in the web management interface of your device.
0 Comments