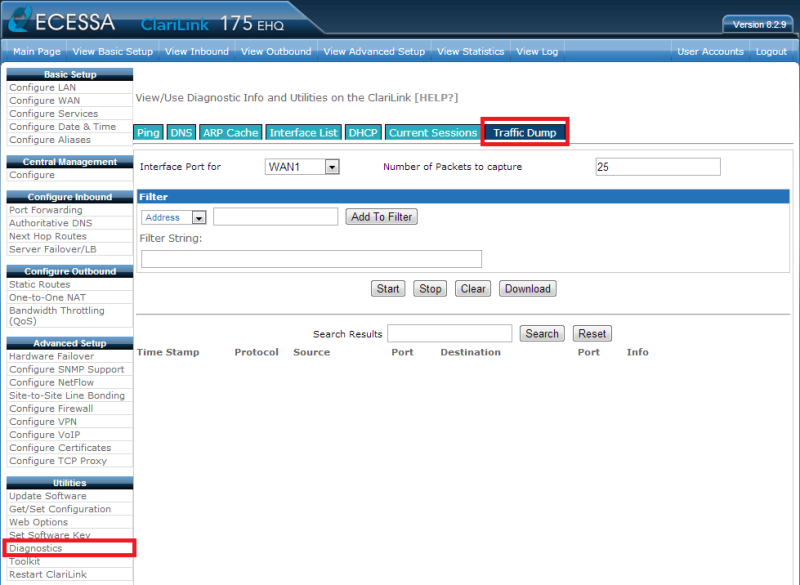
Ecessa’s built in traffic dump utility makes it easy to troubleshoot many common network issues. The utility can be accessed through the web interface by navigating to “Diagnostics” under the Utilities menu and then clicking on the “Traffic Dump” tab.
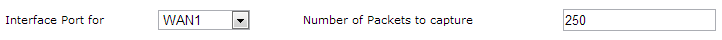
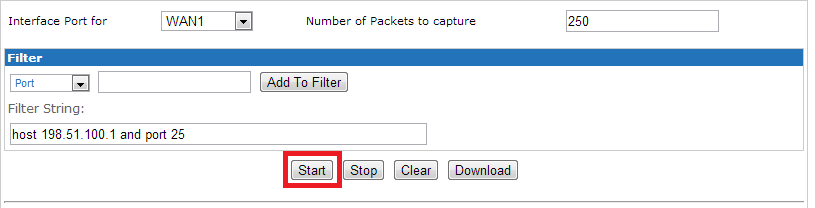
First, select the interface that the traffic dump will be listening on from the pull-down labeled Interface Port for. The Ecessa unit can listen on WAN or LAN ports. Next, define how many packets to capture on the selected interface before the traffic dump stops (minimum is 1 and maximum is 250).
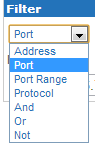
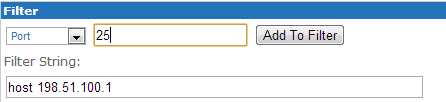
The Filter section allows the user to isolate traffic from or to a specific host, as well as specific types of data (ports or protocols). Multiple filters can be added to a single capture. Prior to starting the traffic dump, use the filter pull down menu to select the properties of the filter you wish to create, clicking on the Add to Filter button for each rule individual rule.
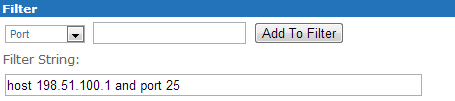
For example, to listen for only port 25 traffic sourcing from 12.34.56.78, select “Address” in the pull-down menu and type “12.34.56.78” on the field next to it, then click Add to Filter. Now select “Port” in the pull-down menu and type 25, click Add to Filter again. The rule will be written out on the line below as “host 12.34.56.78 and port 25.” Modifiers such as “and,” “or,” and “not” can be used to either narrow or expand the capture.

 |
|
After a valid filter string has been added, click the Start button. Each packet on the selected interface port that matches the filter criteria will be displayed along with a time stamp, protocol, source, source port, destination, destination port and a small amount of information related to the packet.
Placing the mouse over a captured packet’s source or destination IP addresses will display its MAC address. The search string can be used to further refine packets displayed from the traffic dump. Use this feature to search for a particular string from any of the captured packet’s properties.
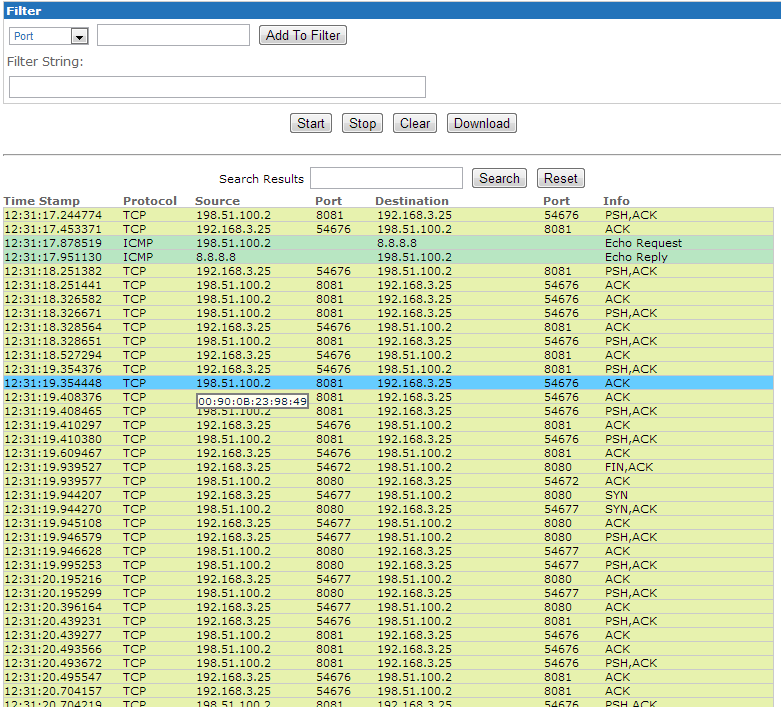
Once a capture has been started, use the Stop button to discontinue the capture before it finishes. The Clear button clears all captured packets. Use the Download button to extract a copy of the full capture in “.pcap” format. This file can be viewed in traffic capture utilities such as Wireshark. Refer to the help link at the top of the page for further assistance.

2 Comments