Overview
Stealth DNS allows the Ecessa appliance to manage inbound redundancy while having an external DNS hosting service handle DNS requests. The following diagram illustrates the example networks for this article.
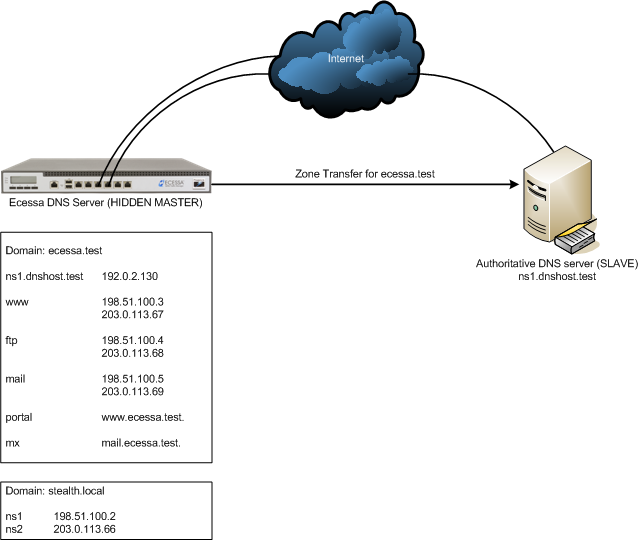
The Ecessa appliance will be configured as a DNS server and will behave as a hidden master. The secondary server(s) will behave as a slave and will answer DNS requests based on the provided zone data from the master. This configuration allows the DNS servers to receive updated zone information based on the Ecessa’s WAN monitoring and dynamic updating of DNS records.
The Ecessa appliance will only listen for DNS traffic on the IP addresses configured as name server addresses. In this scenario, the ecessa.test domain will not include the Ecessa’s WAN IP addresses as name servers so another domain stealth.local is created. Inside this domain, the Ecessa’s WAN IP addresses are set as name servers which will cause the Ecessa to listen for DNS traffic on the configured addresses. This step is important as zone transfers will not work properly otherwise.
Setting Authoritative DNS Servers – Typically, if the Ecessa appliance has DNS configured, it is set as the authority for the domain. In a stealth DNS configuration, the Ecessa appliance will not be configured as an authority (the secondary server(s) will be) nor will it be included as a name server for the domain.
The following diagram shows how stealth DNS configuration handles the process of DNS resolution.
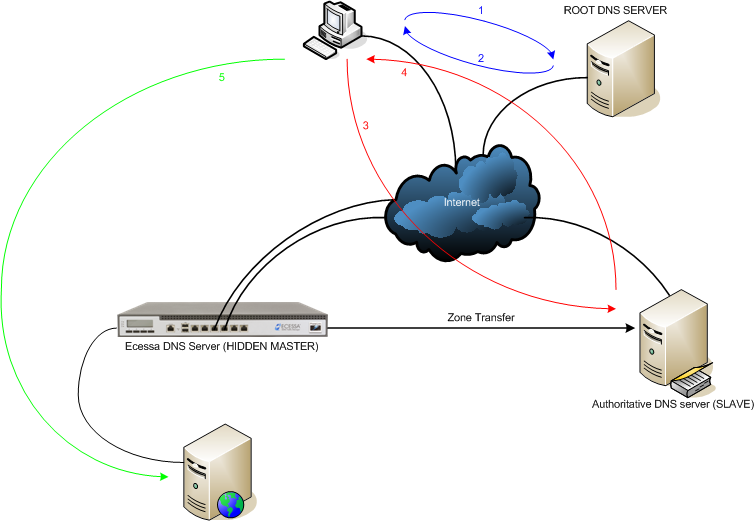
1. The client machine wants to resolve www.ecessa.test so the request is sent to the root DNS servers and follow the lines of authority.
2. The client receives a list of DNS servers responsible for the domain ecessa.test.
3. The request is then sent to one of the authoritative servers for resolution.
4. The given response is based on the zone data provided by the Ecessa (the request is never sent to the Ecessa appliance directly).
5. Once the client receives the appropriate IP address(es) for the host name it can establish a connection to the web server.
Configuring Stealth DNS
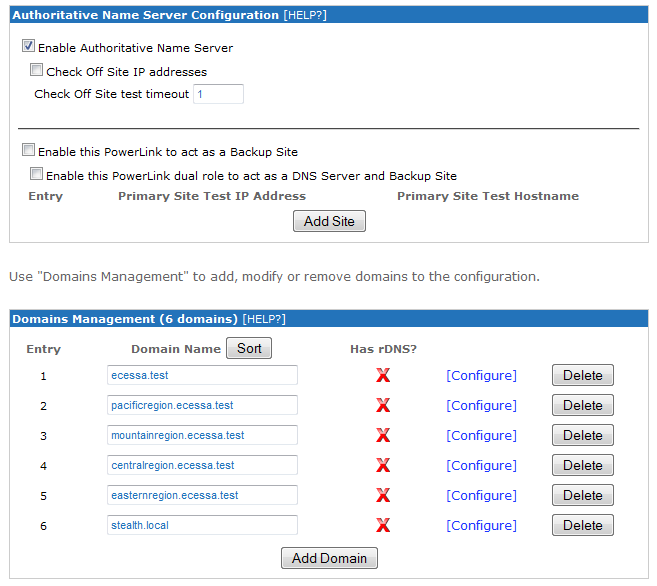
Authoritative DNS page – the Ecessa appliance will need to be configured with the domain(s) for which it will act as the hidden master as well as another “dummy” domain such as stealth.local. For instructions on configuring DNS domains on the Ecessa appliance, please refer to the article “How do I configure Authoritative DNS on an Ecessa appliance?”
Click on Configure for the domain to update. Confirm that the “Enable zone transfers to” setting is enabled and the text field has the appropriate IP address(es) for the backup DNS server (s). Click the Activate button to save the changes.
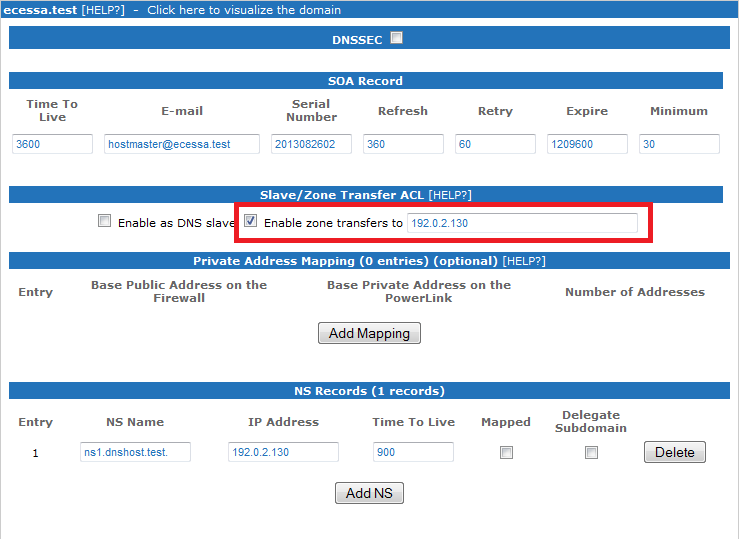
The secondary DNS servers should receive a zone transfer for each of the configured domains and will answer accordingly. The Refresh value in the SOA Record section will determine how frequently the zone will be transferred. The default Refresh value is set to 360 seconds which may be reduced to minimize potential downtime and expedite the propagation of changes.
Testing DNS resolution of a load balanced host record:
C:\> dig @192.0.2.130 www.ecessa.test
; <<>> DiG 9.9.1-P3 <<>> @192.0.2.130 www.ecessa.test
; (1 server found)
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 35596
;; flags: qr aa rd; QUERY: 1, ANSWER: 2, AUTHORITY: 1, ADDITIONAL: 1
;; WARNING: recursion requested but not available
;; OPT PSEUDOSECTION:
; EDNS: version: 0, flags:; udp: 4096
;; QUESTION SECTION:
;www.ecessa.test. IN A
;; ANSWER SECTION:
www.ecessa.test. 30 IN A 203.0.113.67
www.ecessa.test. 30 IN A 198.51.100.3
;; AUTHORITY SECTION:
ecessa.test. 900 IN NS ns1.dnshost.test.
;; Query time: 2 msec
;; SERVER: 192.0.2.130#53(192.0.2.130)
;; WHEN: Mon Aug 26 16:57:45 2013
;; MSG SIZE rcvd: 117
If one of the WAN lines is not available, the Ecessa appliance will update the affected DNS records. Once the Refresh expires, the secondary DNS server will request another zone transfer at which point the server will begin answering requests with the updated information.
For example, the request would be answered with only the available WAN addresses like so:
C:\>dig @192.0.2.130 www.ecessa.test
; <<>> DiG 9.9.1-P3 <<>> @192.0.2.130 www.ecessa.test
; (1 server found)
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 29420
;; flags: qr aa rd; QUERY: 1, ANSWER: 1, AUTHORITY: 1, ADDITIONAL: 1
;; WARNING: recursion requested but not available
;; OPT PSEUDOSECTION:
; EDNS: version: 0, flags:; udp: 4096
;; QUESTION SECTION:
;www.ecessa.test. IN A
;; ANSWER SECTION:
www.ecessa.test. 30 IN A 198.51.100.3
;; AUTHORITY SECTION:
ecessa.test. 900 IN NS ns1.dnshost.test.
;; Query time: 3 msec
;; SERVER: 192.0.2.130#53(192.0.2.130)
;; WHEN: Mon Aug 26 17:36:52 2013
;; MSG SIZE rcvd: 101
0 Comments